The number of heavy DDoS-attacks has increased to record levels
According to a report of Akamai company, in the first quarter of 2016 happened at least nineteen DDoS-attacks, which exceed the capacity of 100 Gbit/s. This is a record. For comparison, during October, November and December of last year has happened only five DDoS-attacks with comparable power.
In early 2016 heavy powered attacks ceased to be a rarity. In January, February and March Akamai has registered as many as six attacks, during which the load exceeded 30 million packets per second, and two attacks in which the load has reached 50 million packets per second.
Attackers are actively using amplification with the help of DNS, NTP, CHARGEN and other similar methods. The principle in all cases is the same: they exploit the features of network protocols to make other people’s servers to bombard the victims with loads of unnecessary information. As a result, the victim gets an excessive load which is many times greater than outbound traffic from the attacker.
The most popular method of this kind was DNS amplification. With this attack the DNS servers receive fake requests from the attacker, that force them to send detailed answers to the victim. Share of attacks using the DNS amplification method was 18%. 12% of attacks used NTP amplification. Third and fourth place went to CHARGEN and SSDP – 11% and 7% respectively.
Only 41% of DDoS-attacks, which were observed by the experts from Akamai during the first quarter of 2016 were limited to a single method. 42% – were combining two methods, and 17% – used three or more methods at the same time. As to resist each method requires its own strategy, this approach makes it difficult to protect against DDoS.

The number of not as powerful DDoS-attacks has also become greater. According to Akamai, the total number of attacks that took place earlier in the year, has increased by 142,14% compared with the first quarter of 2015 and 22.47% compared with the previous quarter. At the same time, DDoS-attacks have become shorter. Whereas in the past they reached the average duration of 24.82 hours, now this figure has decreased by 34.98% and now it is 16.14 hours.
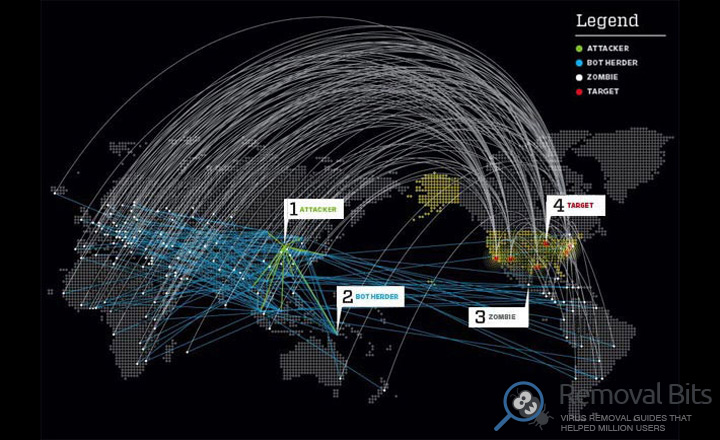
The source of the vast majority of DDoS-attack were the computers located in China, the United States and Turkey. This, however, only shows that these countries have the most infected computers that are able to connect to the malicious botnet. The attackers themselves can be anywhere.
If you don’t want to be a part of malicious botnet you have to keep your computer up to date and always protected by antivirus and firewall. Also, it is recommended to have your computer checked for malware, which you can do with our anti-malware utility.
Related Posts
- Warning: Mac-targeting ransomware
- 60% of Americans are cyber security experts
- Lenovo has fixed vulnerabilities in their computer firmware
- Google and Samsung have fixed the vulnerability Dirty COW in Android firmware
- Hajime Trojan worm written in C can be controlled by P2P and infects IoT-devices
- HDDCryptor – ransomware which can overwrite the MBR on the victim’s computer
- Trojan, disguised as a guide for Pokemon Go has been installed more than 500 000 times!
- Researchers from Sophos have found a hacker, who has been infecting other hackers with his own malware

Great, detailed, step by step instructions. Very helpful, worked perfectly. Thank you! – Halász Domokos
Thank you so much for you clear, comprehensive instructions. I have sent you a donation and now my appreciation for providing great information to help me remove malware myself. I am so excited I did it and I have you to thank – Alexander Schäfer
Excellent information that worked! Thank you very much – Dieter Friedman
This was very intuitive and helpful. Just make sure you follow each step in the correct order. It is time consuming, but very important. Thank you! – Jorma Filatov