How dangerous can GX40 Ransomware be?
According to cyber analysts, we’re are experiencing some sort of a ransomware boom these days. The GX40 Ransomware is just another link in this chain of events. However, this one was made most likely by amateur hackers but still acts according to the main ransomware pattern. We do believe that this malware is still in development and more dangerous version are about to appear soon. That is why you should definitely know how to remove GX40 Ransomware virus.

Interesting fact: GX40 Ransomware is probably a product of beginner programmers due to simplified behavior and information provided in the ransom note. It is still capable of messing up some of your files. In this particular case, all infected files get a new extension of «.encrypted». It is easy to miss that something is wrong and your security along with the data is compromised if you don’t have any anti-malware protection. After finishing the encryption, GX40 Ransomware informs the user with a note that demands a ransom to be paid.
GX40 Ransomware attacks only the desktop files. So there is a high chance you might not lose many valuable files. The malware developers give their victims two days to pay the sum for a decryption key. The amount is rather low – 80 US dollars – but don’t fall scammers’ promises. They will try to threaten you, saying that all corrupted files will be deleted along with the private decryption key.
It is a common practice to threaten victims and making them think that they are out of options. There are no guarantees that cyber criminals will actually unblock your computer and restore the data. Plus, you will become a sponsor for next attacks contributing to the development of newer viruses and malicious software like this one. As we mentioned above, GX40 Ransomware is in the development stage, so it is possible we will see a decryption program created by the virus experts. But if you don’t want to wait for a solution, you should concentrate on the GX40 Ransomware removal guide created by our analysts.
We still don’t have a full list of the main spreading techniques for this ransomware, but it is safe to say that most common strategies are in use. We already know that GX40 also utilizes distribution with the Trojans help (Gen:Heur.Ransom.HiddenTears.1, Win32.Trojan-Ransom.Filecoder.P@gen, Ransom_CRYPTEAR.SM). And traditional malware spam is on the list too. We remind you to be extra cautious when dealing with unknown sources and senders. Stay away from any executable files of unknown origin and download updates for your software from official sites only.
And now back to solving the problem. There are two ways to get rid of the GX40 Ransomware. You can do it manually if you know where the original malicious file is hidden. But it might take time. Plus, if you don’t know where to look you can accidentally delete wrong files. To avoid this, we recommend using a reliable anti-malware program like Plumbytes Anti-Malware or SpyHunter. If your computer is infected with GX40 Ransomware, it will be eliminated along with other threats found. Having an additional protection against cyber-attacks is highly recommended because other threats might come your way after previous are neutralized.
GX40 Ransomware Removal Instruction
Automatic Removal for GX40 Ransomware
Symptoms of GX40 Ransomware infection on your computer can be: computer crashes, unusual homepage or search engine on your browser, unwanted pop-up ads and advertising banners. We recommend to download our automatic removal tool. This removal tool has been tested for GX40 Ransomware threat removal and it is easy to use.
Removal GX40 Ransomware with the help of technical experts
expert technical support

Manual Removal Instruction for GX40 Ransomware
-
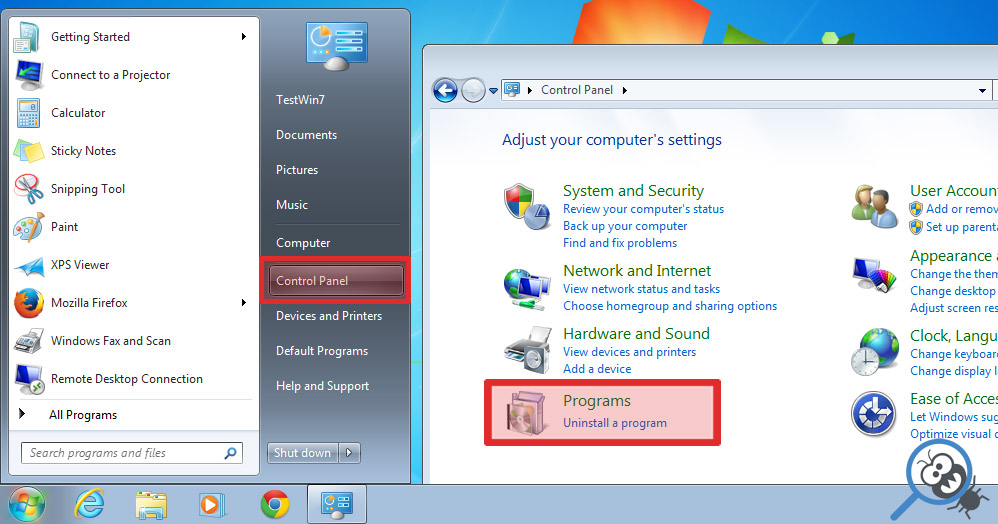
Click on the Start button in the left lower corner and select → Control Panel. After that find the Programs and Features (if you are running Windows XP , then click on Add/Remove Programs).
-
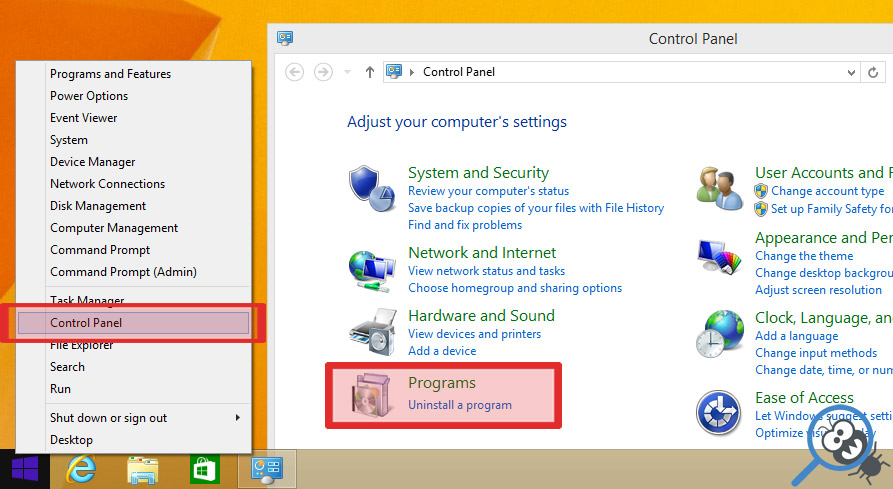
If you are running Windows 8 or Windows 10 operating system , then right-click on the Start which is in the lower left corner of the screen. After that select Control Panel and go to Programs/Uninstall a Program.
-
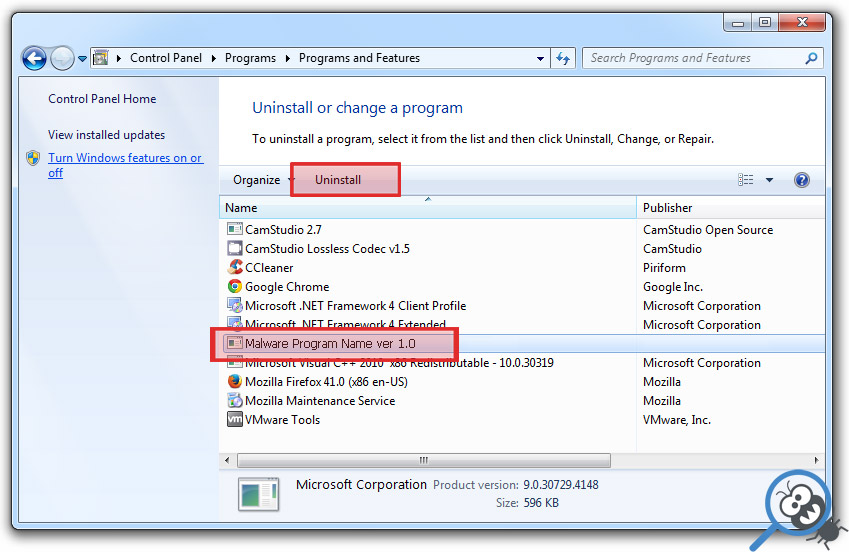
In the list of installed programs find the GX40 Ransomware or any other recently installed suspicious programs.
-
Click on them to select and then click on Uninstall button to remove them.
-
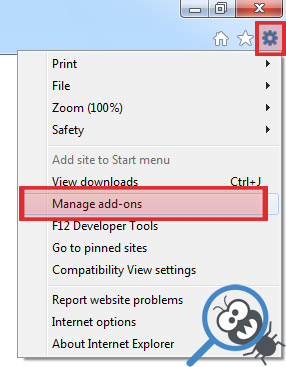
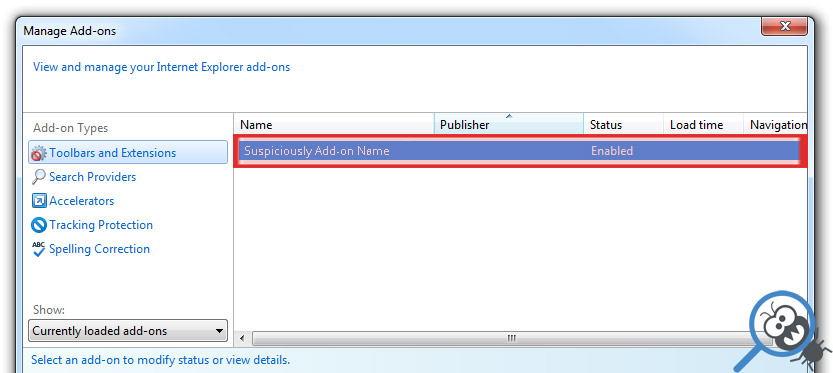
Open Internet Explorer, click on the Gear icon (IE menu) on the upper right corner of the browser and select Manage Add-ons.
-
You will see a Manage Add-ons window. Now, find the GX40 Ransomware and other suspicious add-ons. Disable them by right clicking and selecting Disable:
-
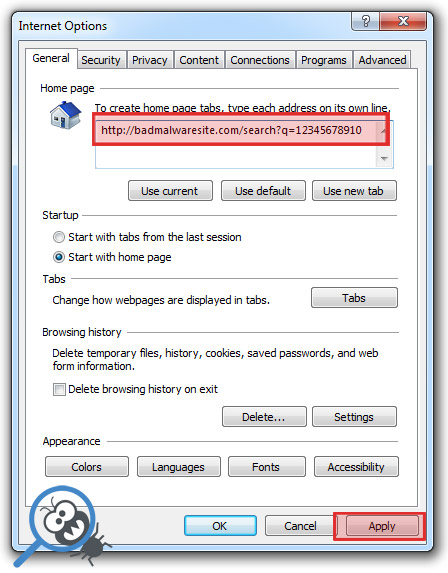
Click on the gear icon (menu) on the upper right corner of the browser and select Internet Options.
-
On General tab remove unwanted URL and enter your desired domain name such as google.com. Click Apply to save changes.
-
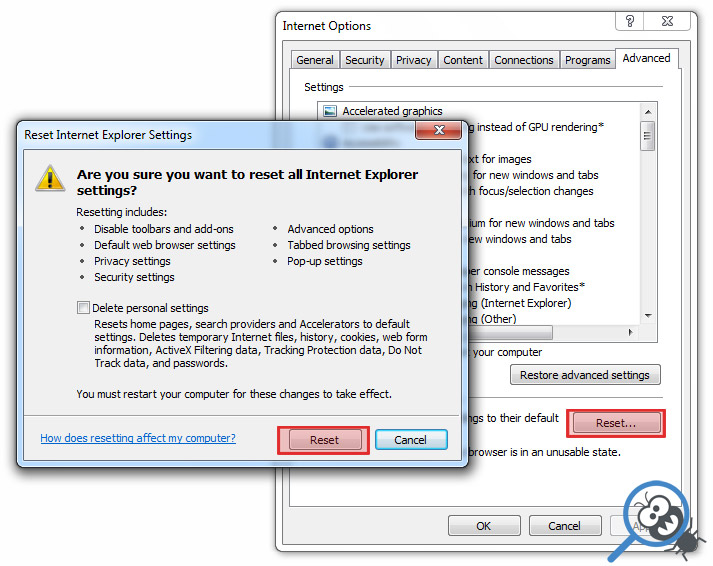
Click on the gear icon (menu) again and chose Internet options. Go to Advanced tab.
-
Now click on Reset button, the new window should appear. Select the Delete Personal settings option and click on Reset button again. Now you have deteled GX40 Ransomware completely.
-
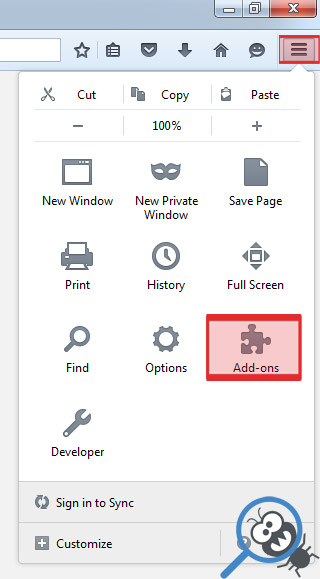
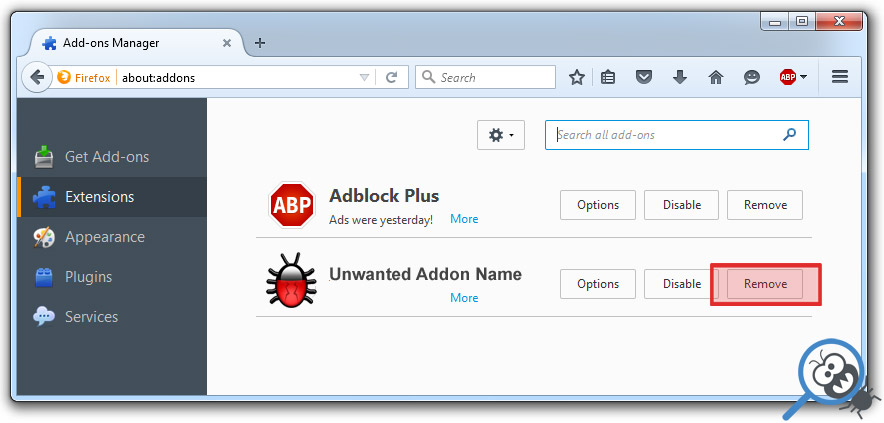
Open Mozilla Firefox, click on the menu icon which is located in the top right corner. Now select Add-ons and go to Extensions.
-
Now you can see the list of extensions installed within Mozilla Firefox, simply select GX40 Ransomware and other suspicious extensions and click on remove button to delete them.
-
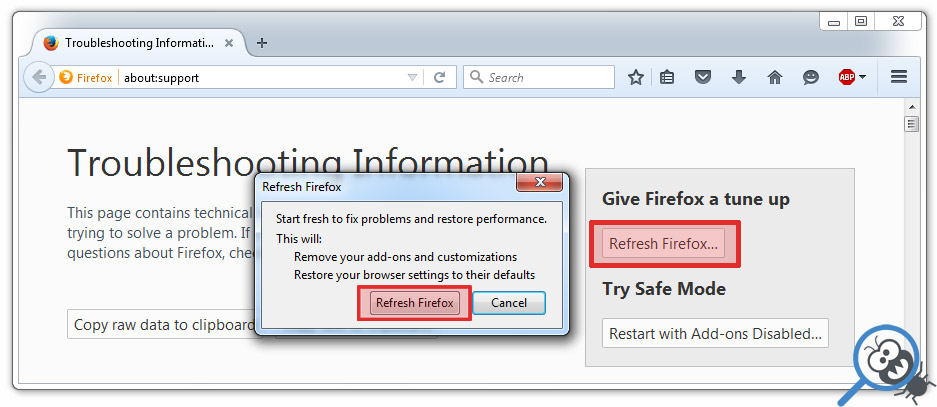
Click on the Firefox menu icon which is on the upper left corner of the browser and click on the question mark. Now, choose Troubleshooting Information option.
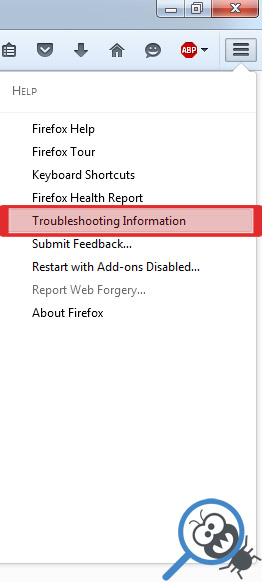
-
New windows will pop-up where you can see Refresh Firefox to its default state message and Refresh Firefox button. Click this button to remove GX40 Ransomware completely.
-
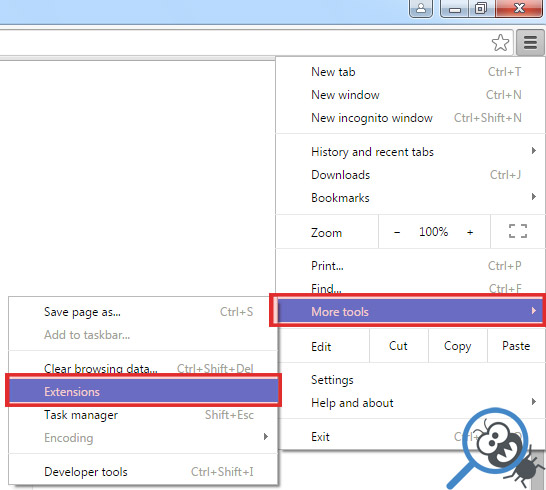
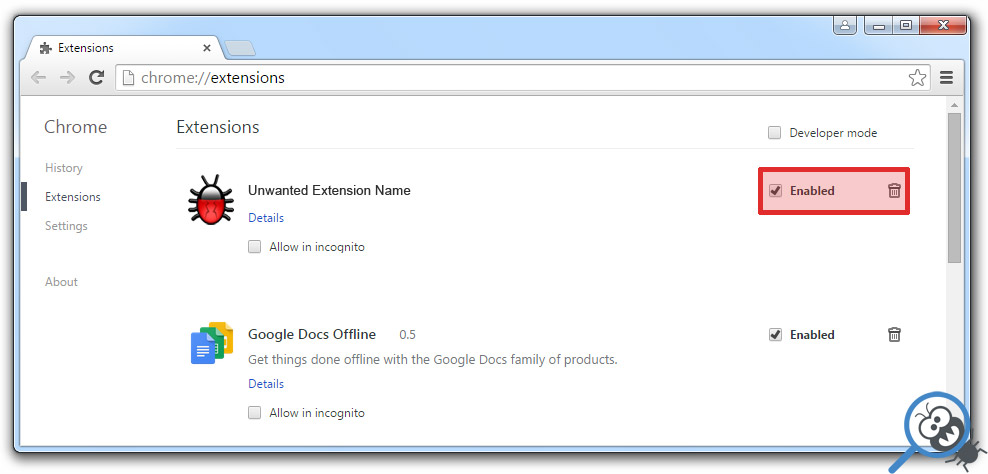
Open Google Chrome, click on the menu icon in the upper right corner and select More Tools and then select Extensions.
-
Now, find the GX40 Ransomware and other unwanted extensions and click on trash icon to delete them completely.
-
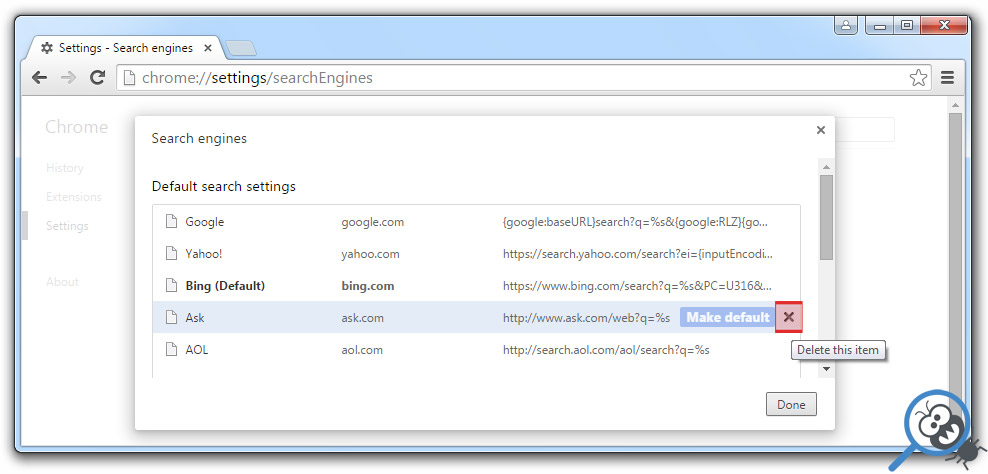
Click on menu icon once again and select Settings and then Manage Search engines it will be right under the Search section.
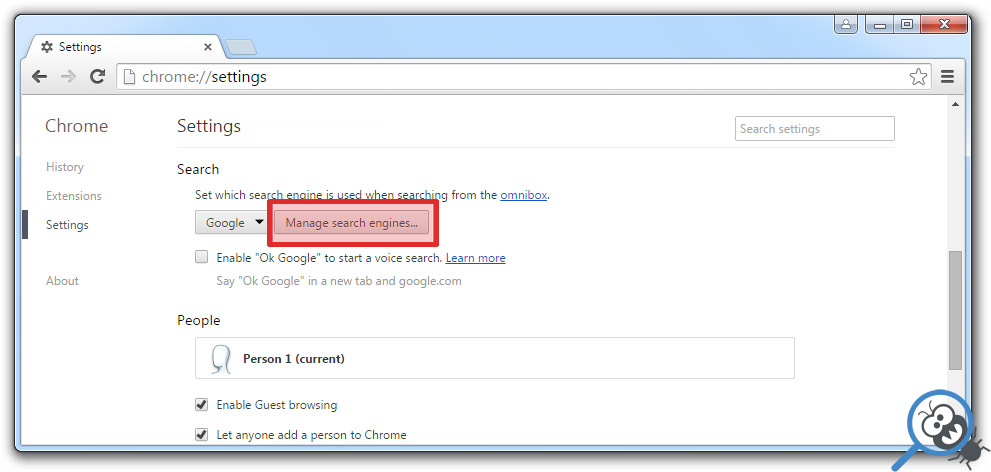
-
Now you will see all of the Search Engines installed in your browser. Remove any suspicious search engines. We advise you to leave only Google or your preferred domain name.
-
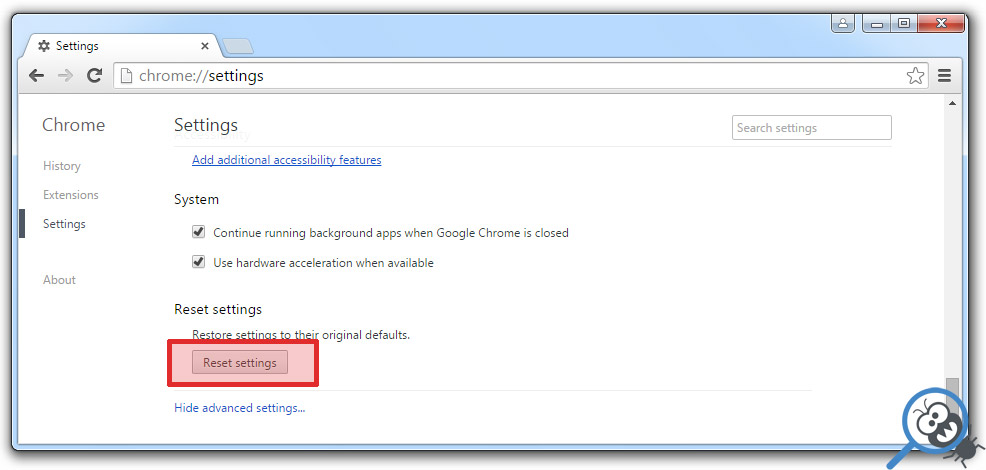
Click on menu icon which is on the top right corner of your Google Chrome browser. Now select Settings. Click Show Advanced Settings...
-
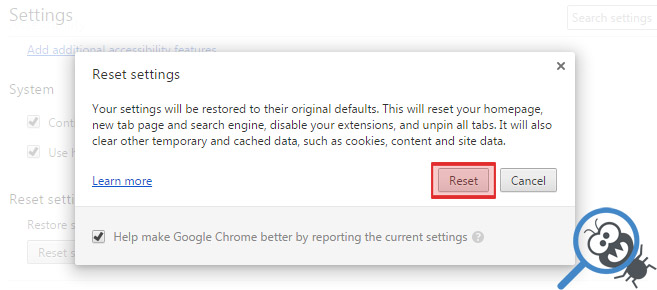
Scroll down to the end of the page and find there Reset settings and click on it.
-
New window will pop-up where you click on Reset button to confirm the action and remove GX40 Ransomware completely.
After performing all of the steps above you should have all of your web browsers clean of the GX40 RANSOMWARE and other suspicious add-ons and extensions. However to complete the removal procedure we strongly advise to scan your computer with antivirus and anti-malware tools like SpyHunter, HitmanPro 32-bit, HitmanPro 64-bit or Malwarebytes Anti-Malware. Those programs might help to you find registry entries of malware and remove them safely.
Related Posts
- How to kill Search.searcheasysta.com browser hijacker?
- Why you should stay away Www-searches.net
- All you need to know about Spoutly ads
- Is “Notice From Microsoft Corporation” real?
- Fake WindowsUpdater Ransomware removal guide
- Chromesearch1.info browser hijacker removal guide
- FinalRansomware removal guide
- How to delete 6789.com browser hijacker?

Thanks very much for providing me instruction about how to get rid of GX40 Ransomware – Markus Lemond
You are the only ones who were able to remove the GX40 Ransomware from my PC running Windows 8. I had tried four or five different sites and none were as effective as yours. I will recommend your site to anyone – Joe Edson
GX40 Ransomware was bothering me every time I turn on my computer, now the problem is gone – Arthur
GX40 Ransomware has taken over my Mozilla Firefox! This is the second time! Thanks god I found your website with simple step by step instruction – Travis Golbert