Creator of Locker trojan apologized to all
An interesting story happened with the Locker Trojan that was recently activated and encrypted files on thousands of users’ computers. Locker was deactivated and have been hiding on users’ computers and waiting for command. Suddenly it was activated on all infected computers simultaneously. This is a very smart tactic which allows an attacker to increase the success rate of attack.
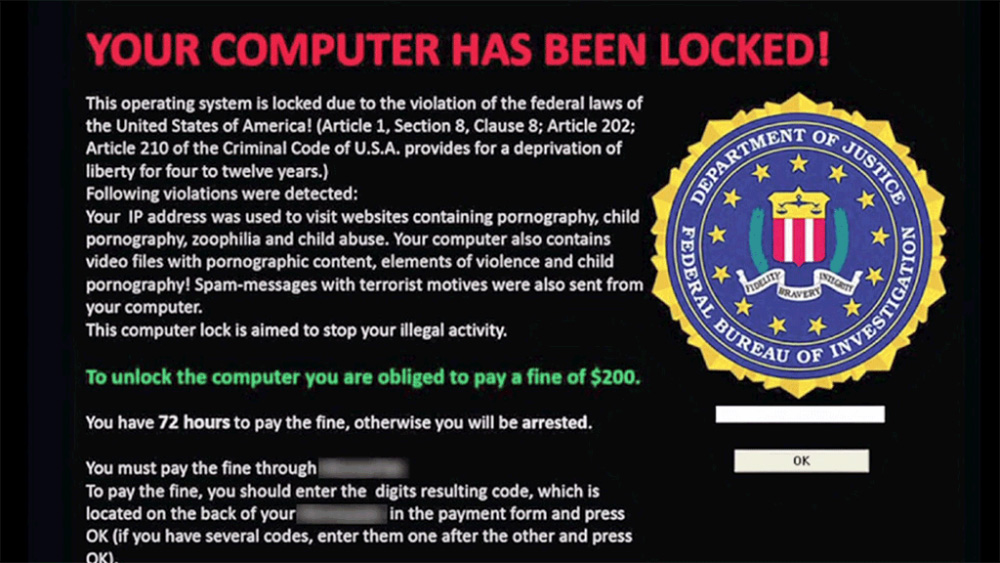
Recently, Locker was activated and demanded from every infected user the amount of 0,1 Bitcoin (around $24). But on May 30th on the Pastebin website a message appeared saying “I am the author of Locker Trojan and I am very sorry for what happened. I never wanted to release it”.
The author gave a link to Mega file hosting where he uploaded a file with 127,5Mb size with dump of the entire database. There are various Bitcoin addresses, public and private keys of each victim. So, the infected user can find on his computer the address where the ransom should be sent, after that he can find the corresponding key in that database dump file and use it to decrypt files and unlock his computer. Moreover, the author has promised to launch the automatic procedure that will unlock and decrypt files on every infected computer.
Experts find it difficult to explain this behavior of repentant hacker. They think that the author could be under the pressure of law enforcement agencies.
Related Posts
- Windows is no longer the most popular OS
- Warning: Mac-targeting ransomware
- 60% of Americans are cyber security experts
- Lenovo has fixed vulnerabilities in their computer firmware
- Google and Samsung have fixed the vulnerability Dirty COW in Android firmware
- Hajime Trojan worm written in C can be controlled by P2P and infects IoT-devices
- HDDCryptor – ransomware which can overwrite the MBR on the victim’s computer
- Trojan, disguised as a guide for Pokemon Go has been installed more than 500 000 times!

Thank you – this was very complete and most importantly – it worked. Other things I tried, including through my Internet service provider tech support did not work – Mike Black
Thanks for taking the time to make this working guide. It was very helpful – Anne F. Gosselin
Great experience! – Laura
This was very intuitive and helpful. Just make sure you follow each step in the correct order. It is time consuming, but very important. Thank you! – Jorma Filatov